Connect to Azure AD
Connect and integrate your Azure AD user store into your AdminX tenant. Once integrated, all your Azure AD users can be managed from AdminX.
Prerequisites for Azure
AdminX and BlockID integrate with Azure AD natively using Microsoft Graph. To set up this integration, we need to create a few things in Azure.
Please ensure that your Azure environment has permission to perform the following steps
Creating the Application Registration
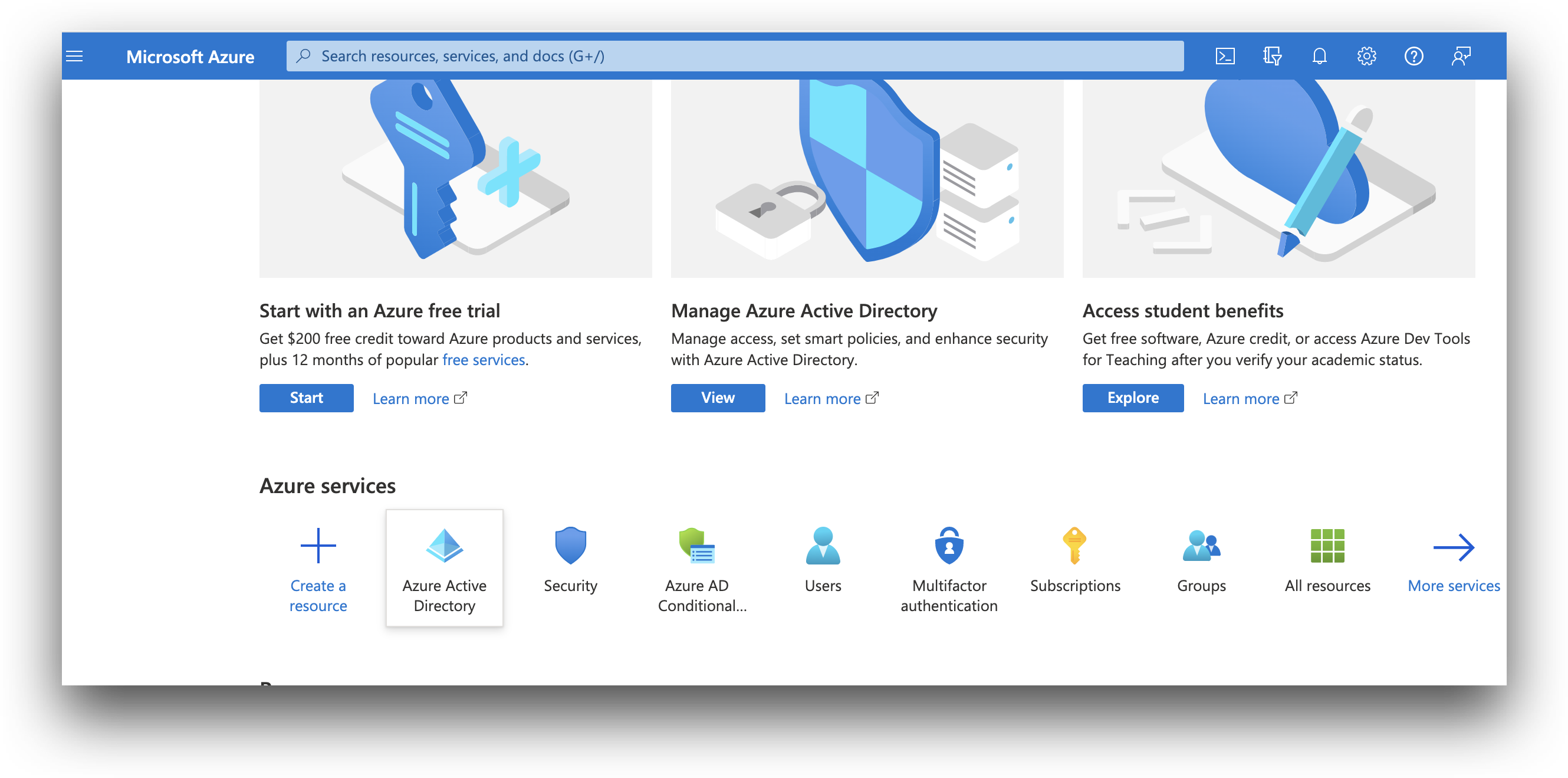
Navigate to https://portal.azure.com/ and log in using your Azure credentials. Once you are logged in, scroll down to Azure services.
Click Azure Active Directory
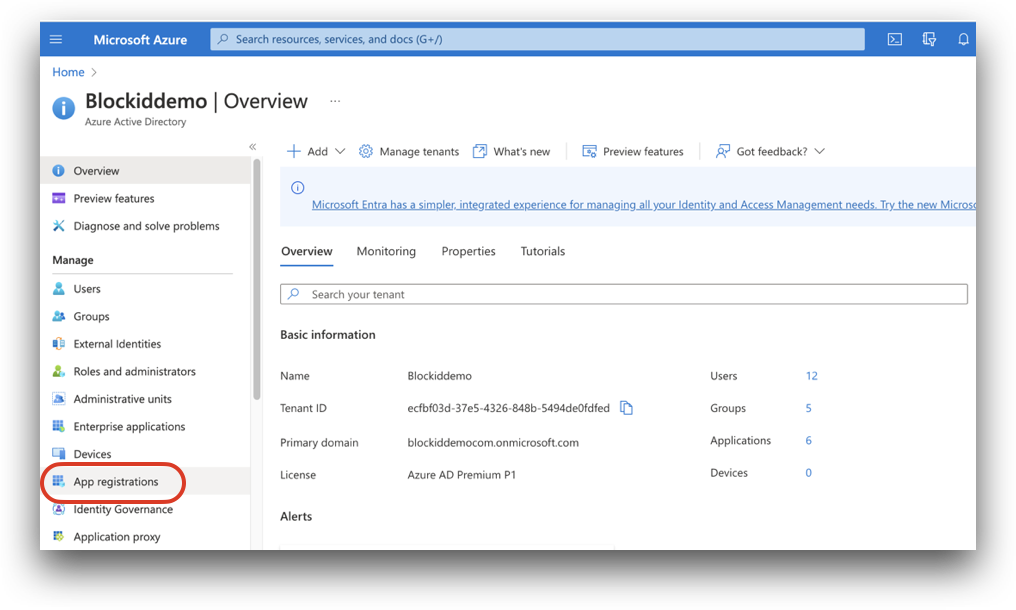
From the application Overview page, click the App registrations link, located partway down on the left-hand menu, under the section titled Manage
From the App registrations page, click New registration
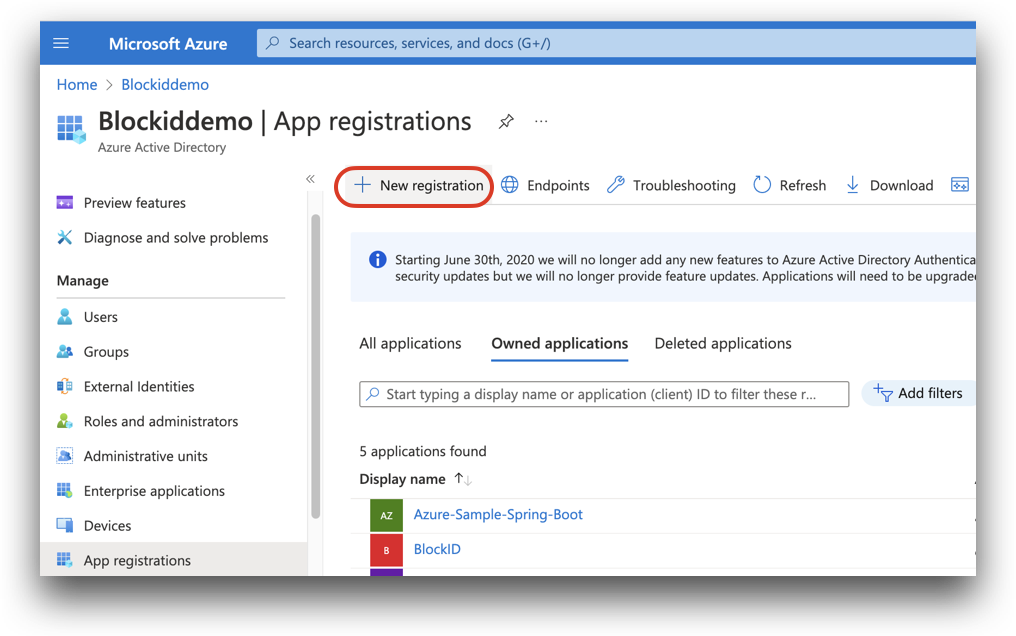
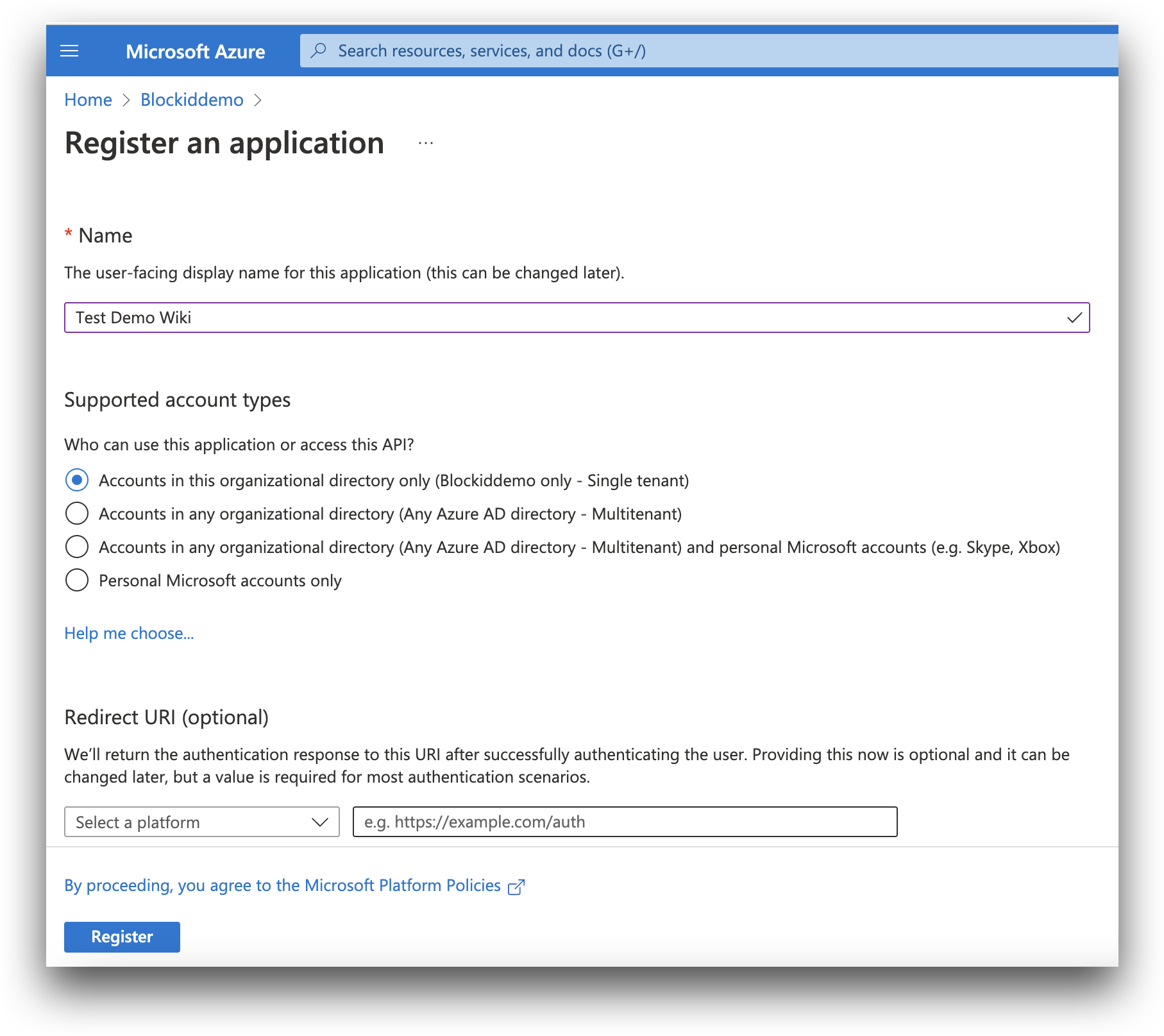
You should now be on the page titled Register an application.
Enter a user-facing display name for your application. For this example, we are using the name Test Demo Wiki.
Under Supported account types, leave the first option selected - Accounts in this organizational directory only (application name only - Single-tenant)
Leave the Redirect URI blank.
Review your selections and then click Register
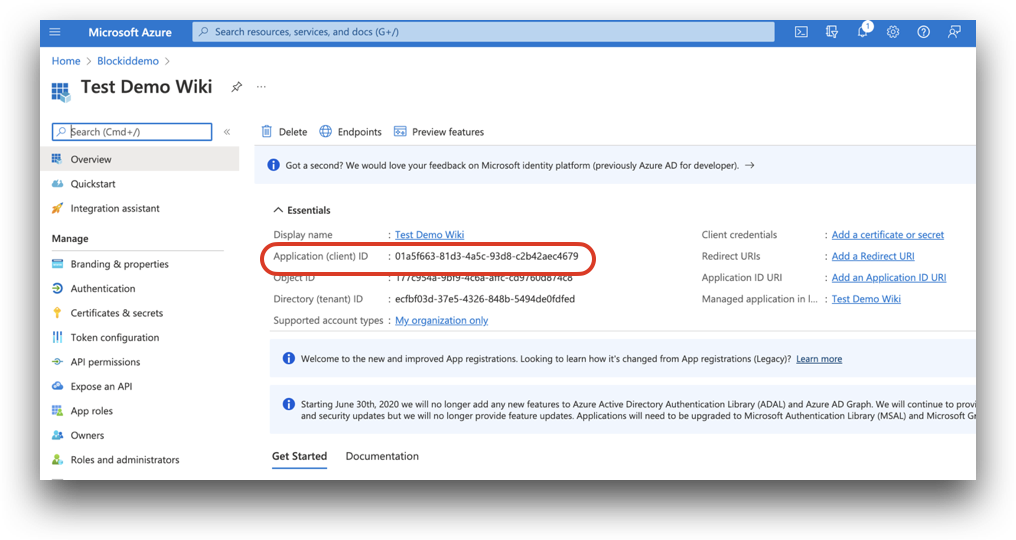
Once the app is registered, you will be redirected to the page listing various details. Make a note of or copy the Application (client) ID as we will need this to configure AdminX for Azure AD.
Creating the Application Secret
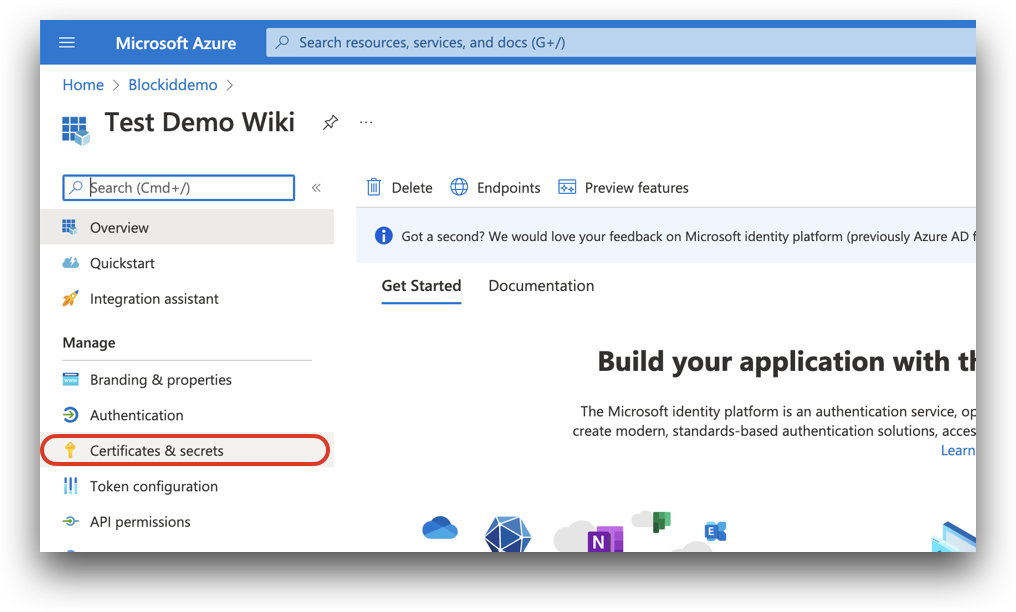
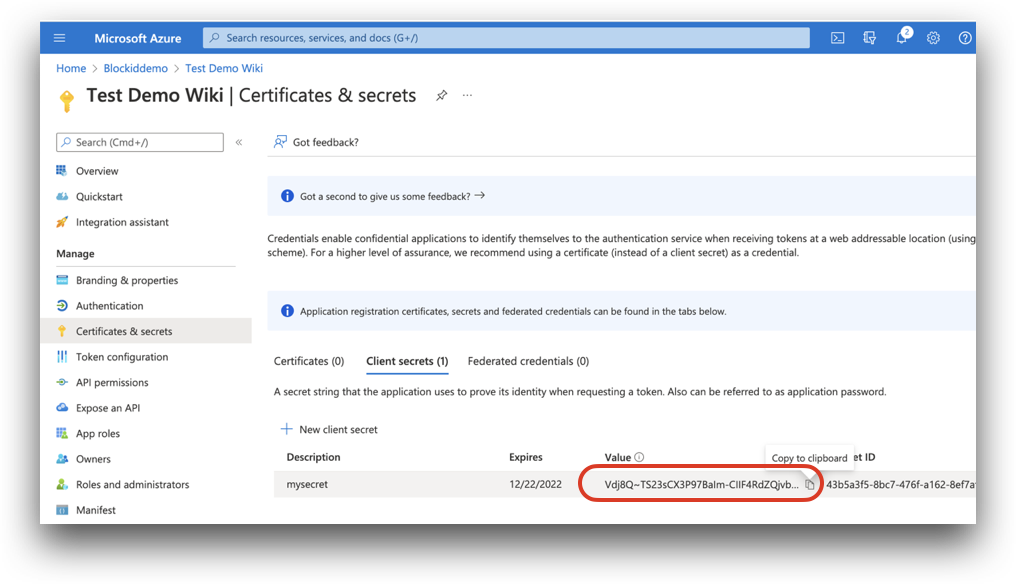
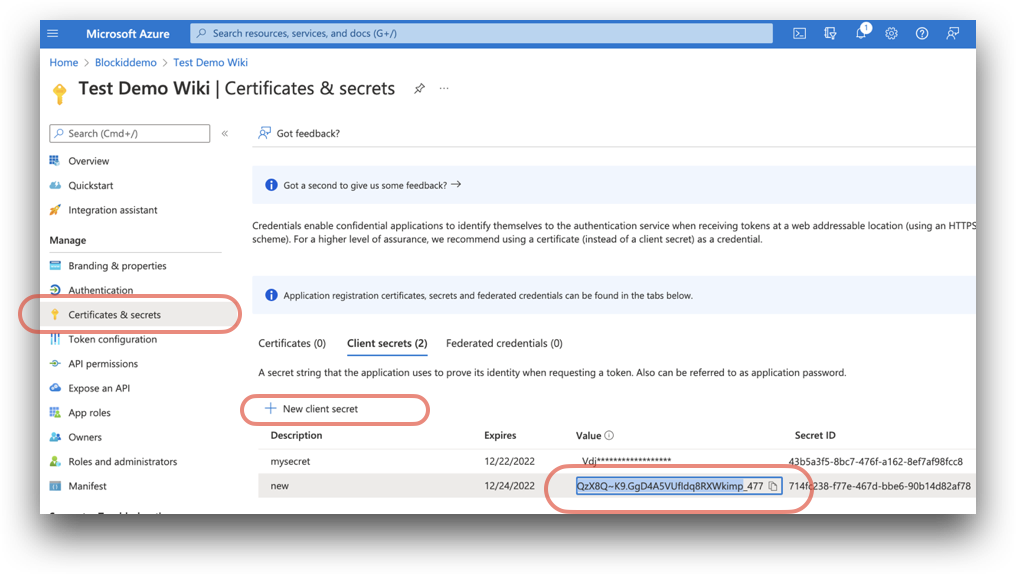
From the same application overview page, click the Certificates & secrets link located on the left-hand menu, under Manage.
From Certificates & secrets click New client secret. Enter a name in the Description box, and select how soon the secret should expire.
Click Add.
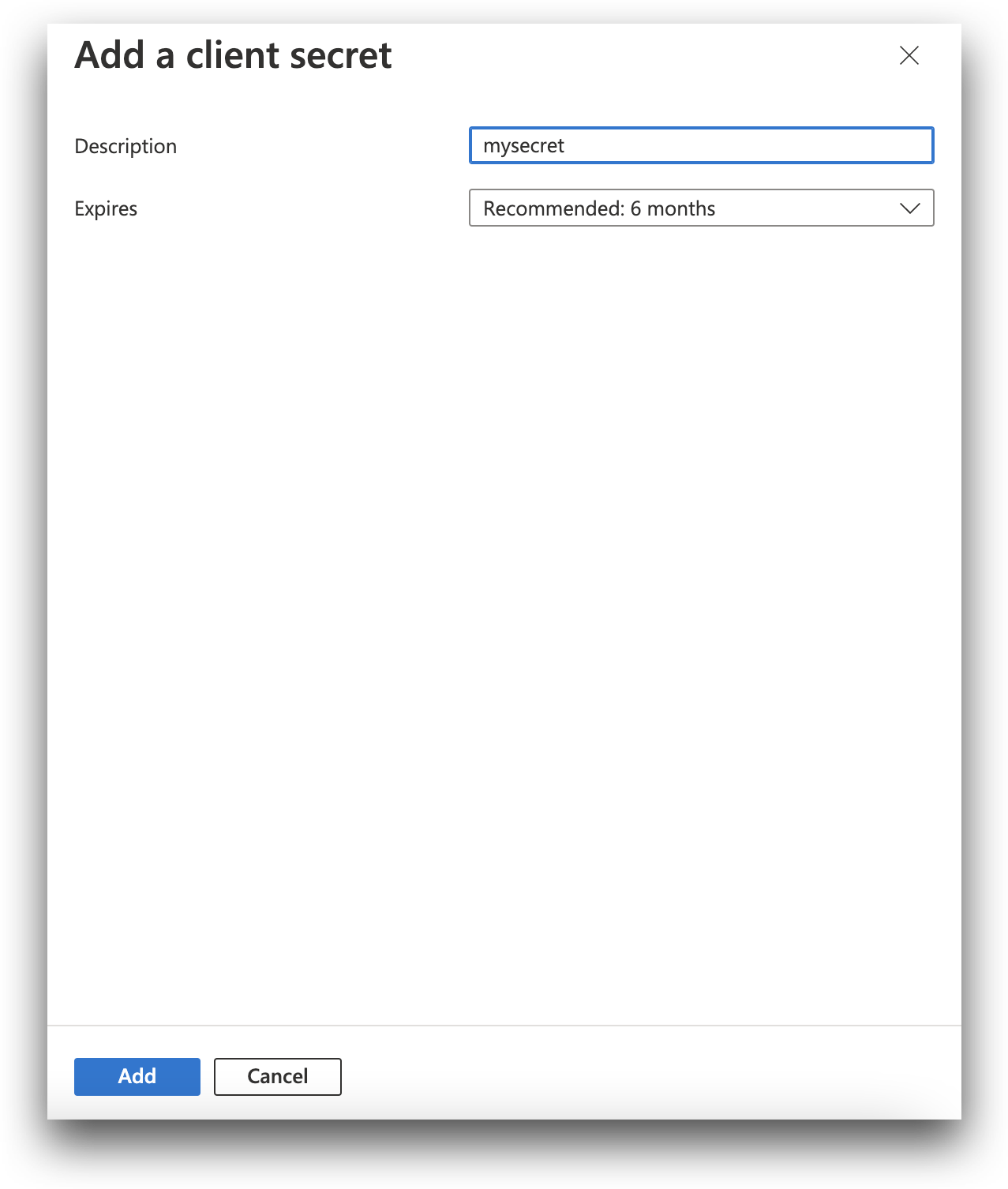
You will now see your secret listed under Client secrets. Make a note of, or copy the Value parameter. We will need this secret to configure AdminX for Azure AD.
Creating the Application Permissions
Next, we need to ensure the Allow public client flows option is enabled. Click the Authentication link located on the left-hand menu under Manage.
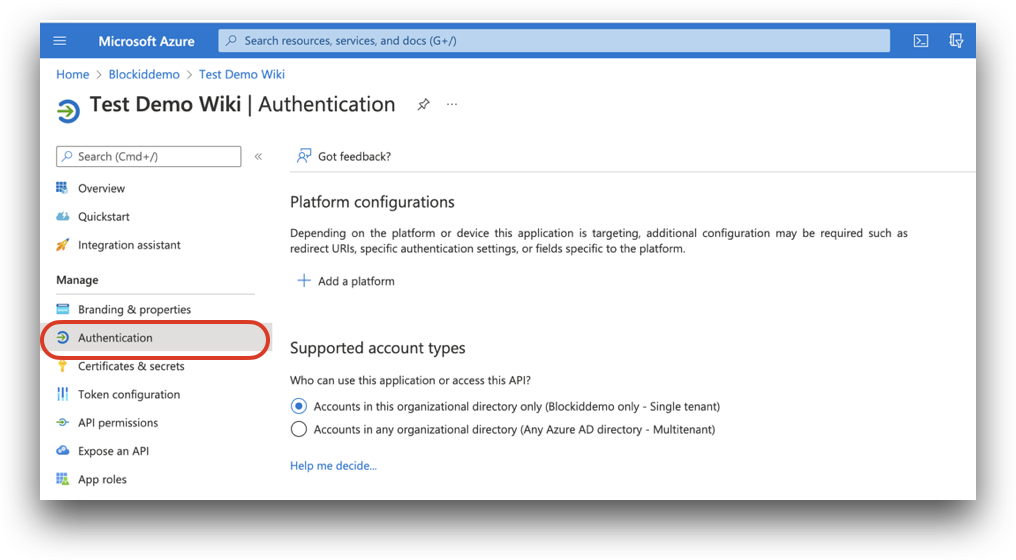
Scroll down to Advance settings, and toggle the Allow public client flows option to Yes.
Double-check that Yes is highlighted as shown, and click Save.
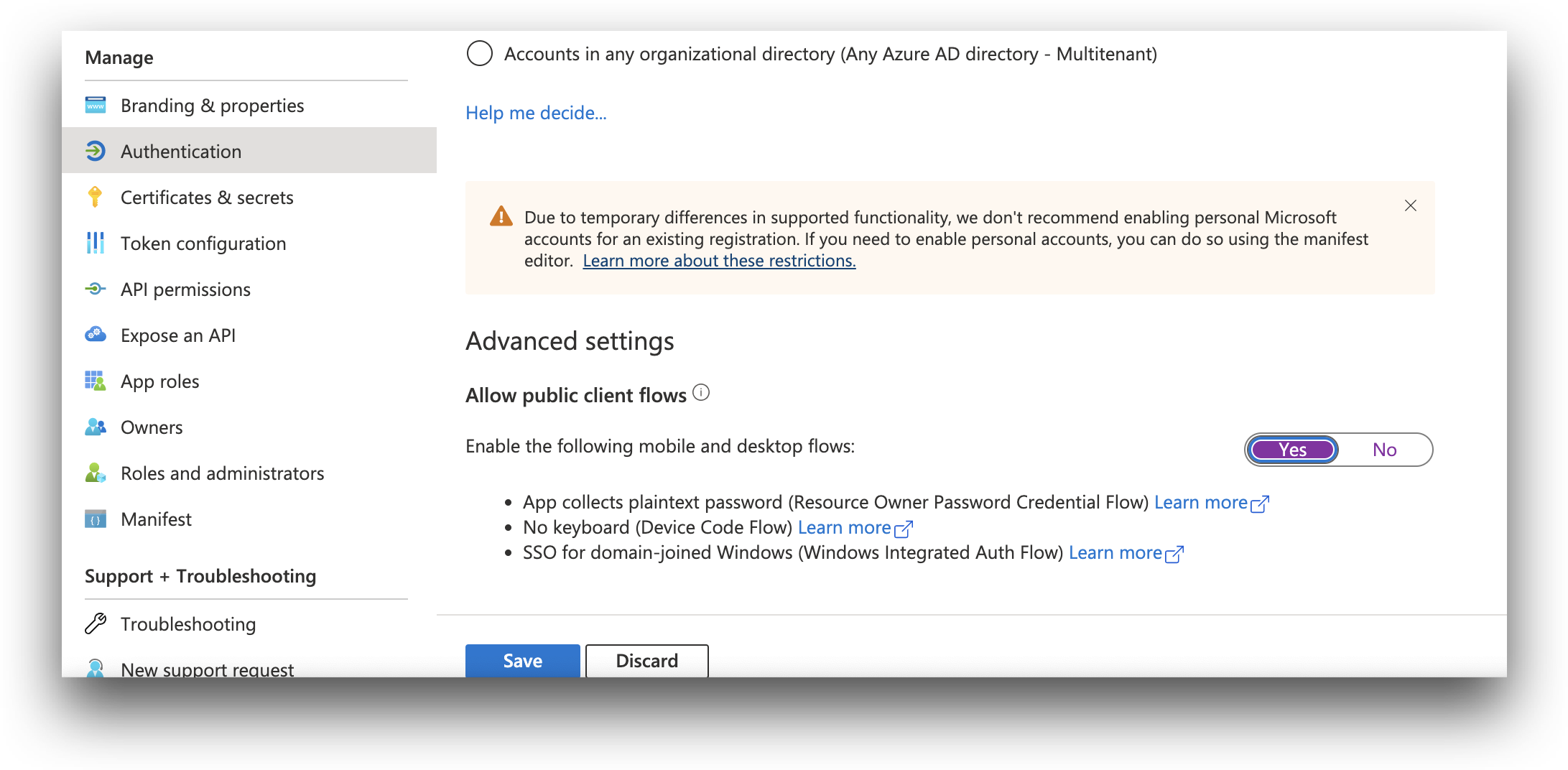
The Allow public client flows option must be set to Yes to use Azure AD in AdminX
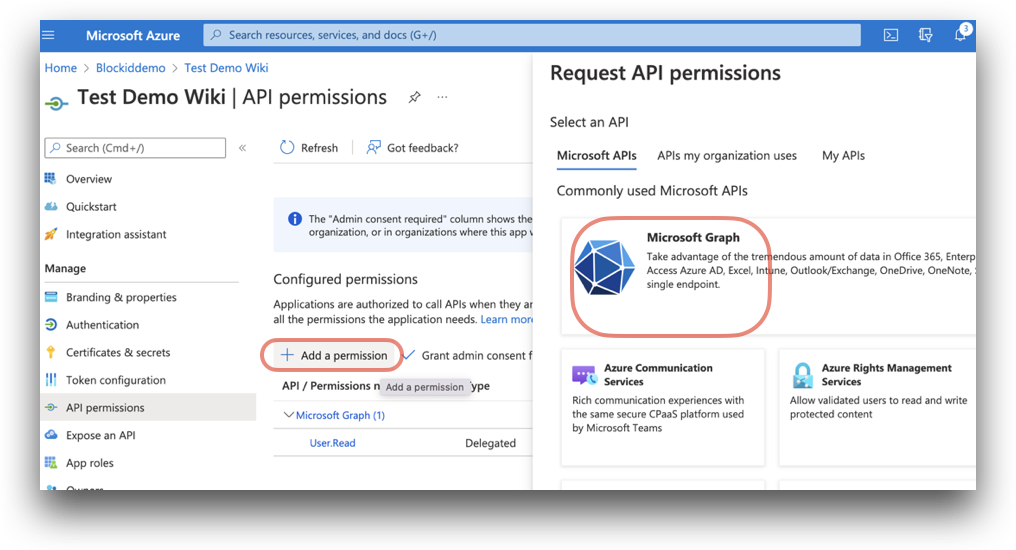
To continue, click the API permissions link located on the left-hand menu under Manage.
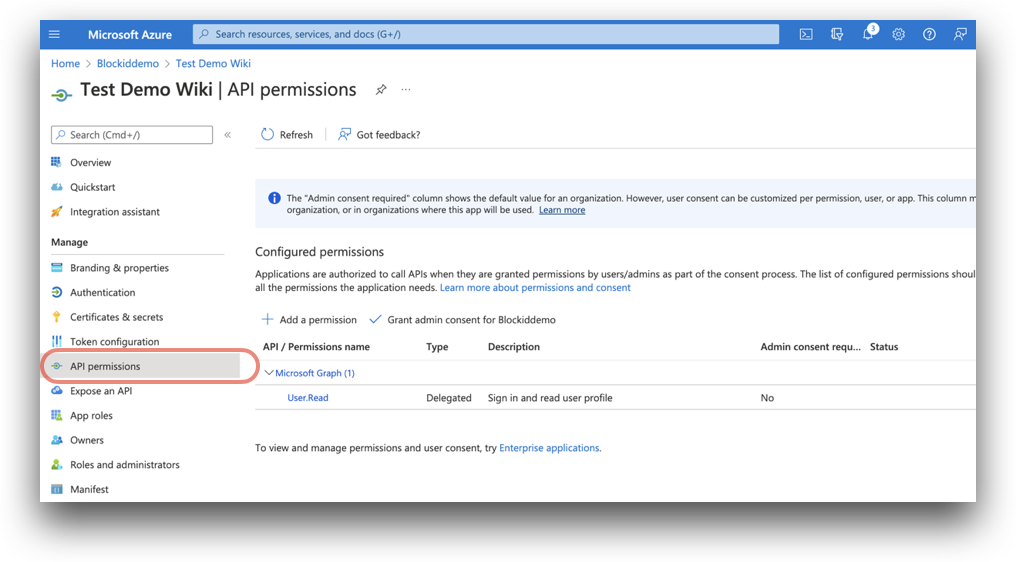
Once on the API permissions page, click Add a permission. A window titled Request API permissions will pop up. Select Microsoft graph, the largest of the available icons.
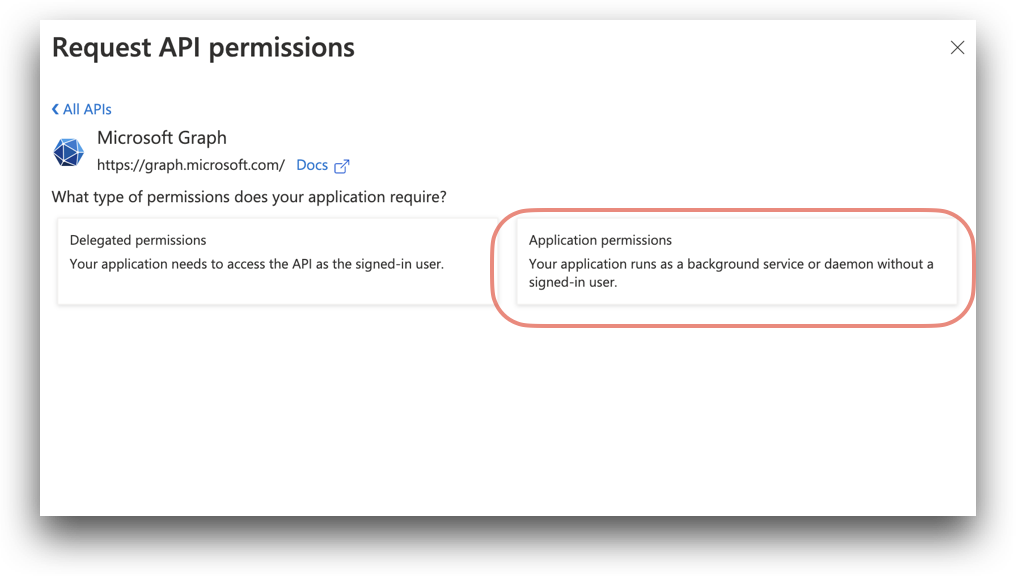
Click Application permissions
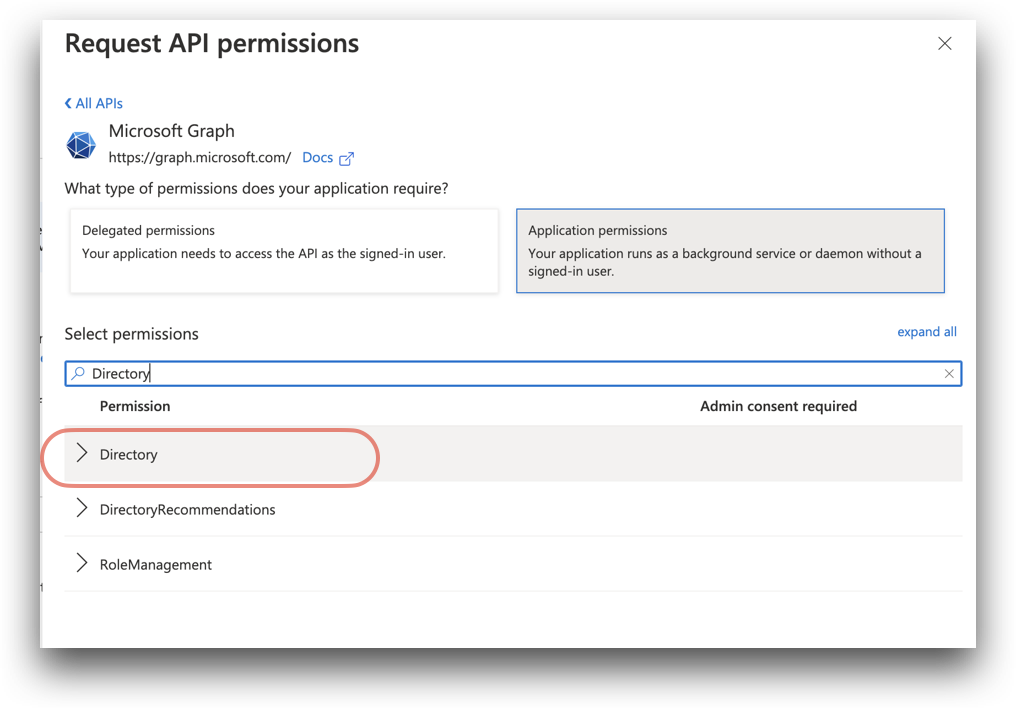
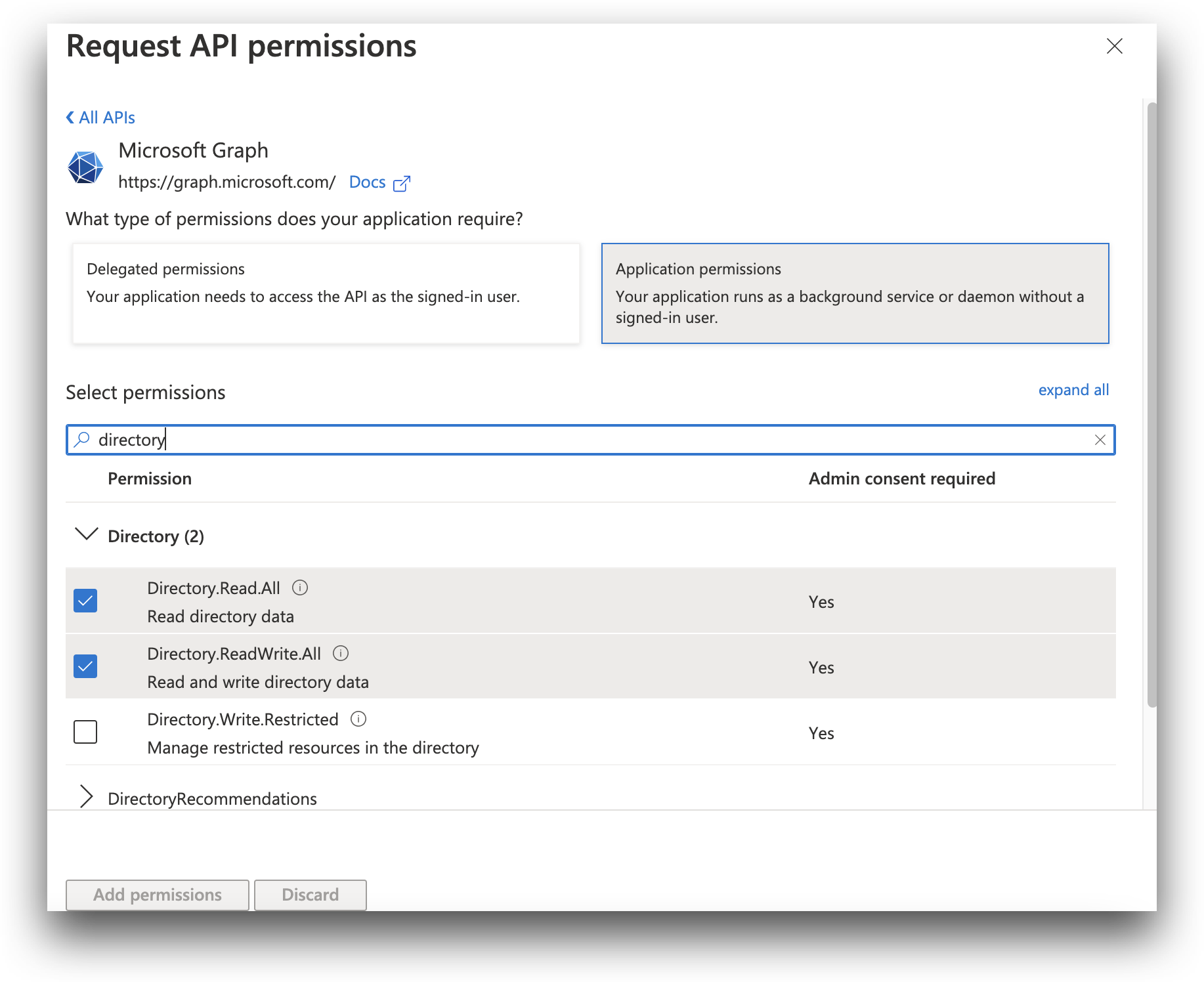
Under Select permissions, there is a search box. Search for the following permissions in the search box by entering the first word - such as Directory - and by then expanding the Directory result to see the full list of permissions:
If you wish to enable reading and writing to the user directory - being able to add or delete users - enable the following permissions:
Directory.Read.allDirectory.ReadWrite.allUser.ReadUser.ReadWrite.all
If you only wish to read from the user directory and to not be able to add new users, instead enable the following permissions:
Directory.Read.allUser.ReadUser.Read.all
When you are finished, click Add permissions.
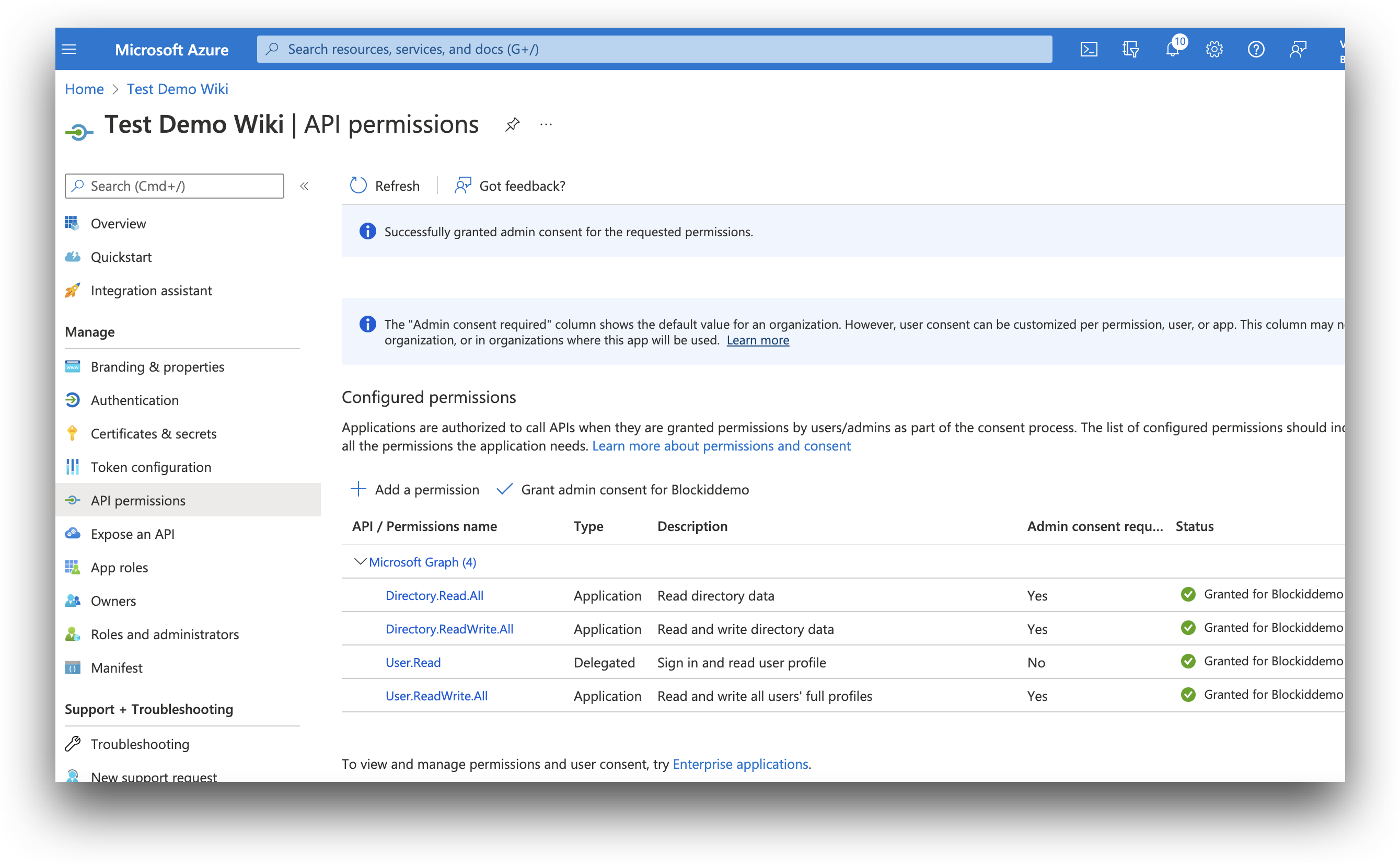
The permission will need to be approved by an administrator before it can be used. To grant consent, click Grand admin consent for [your application].
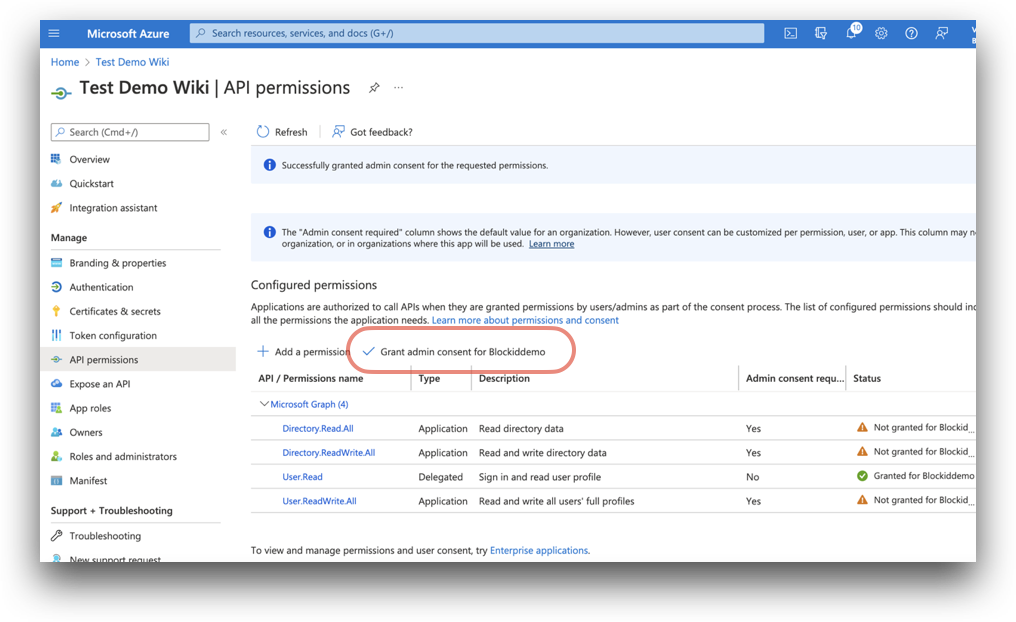
After approving consent, the status will change to Granted.
Gather Information Needed for AdminX
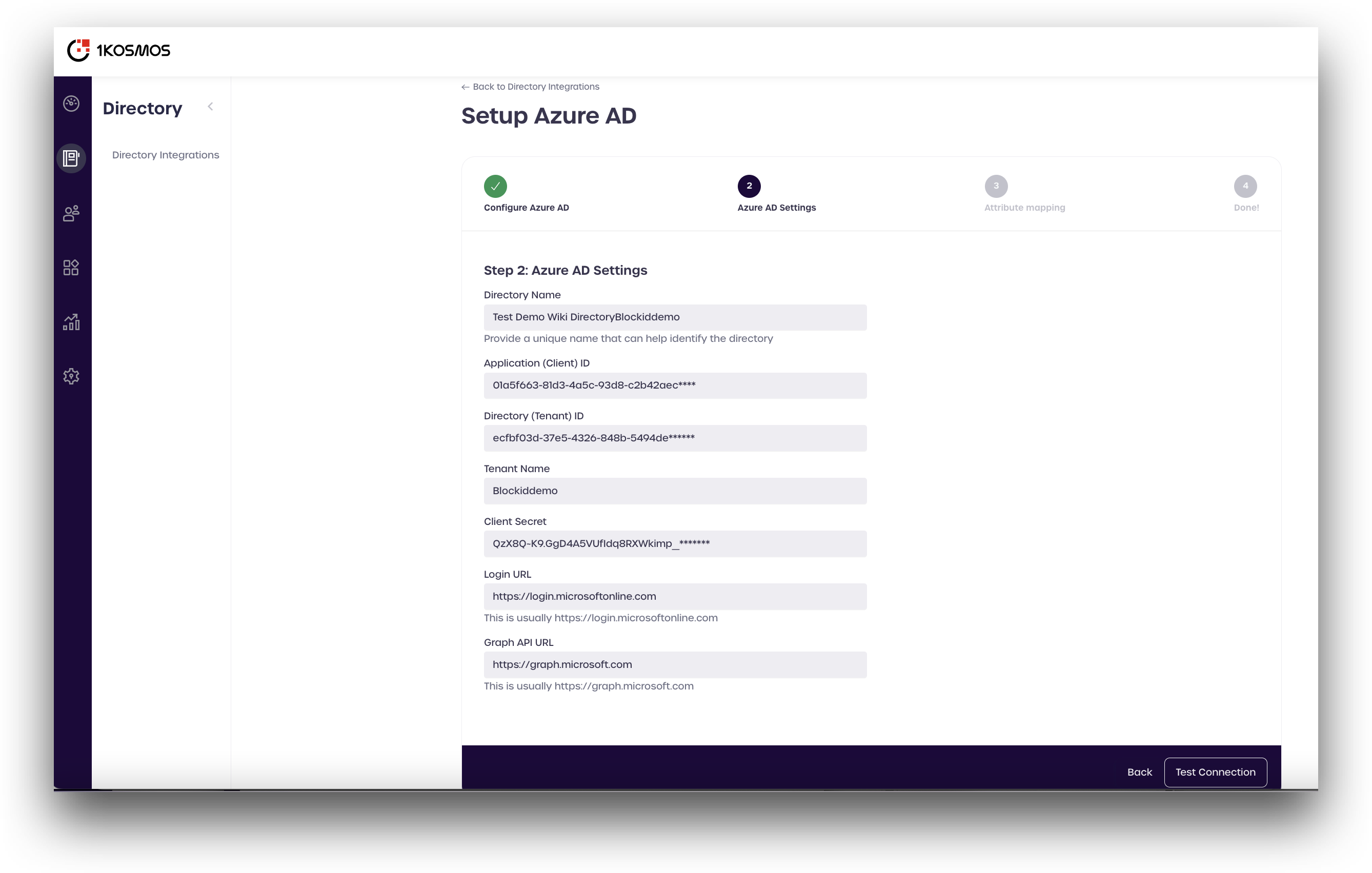
The following items are needed to configure Azure AD in AdminX.
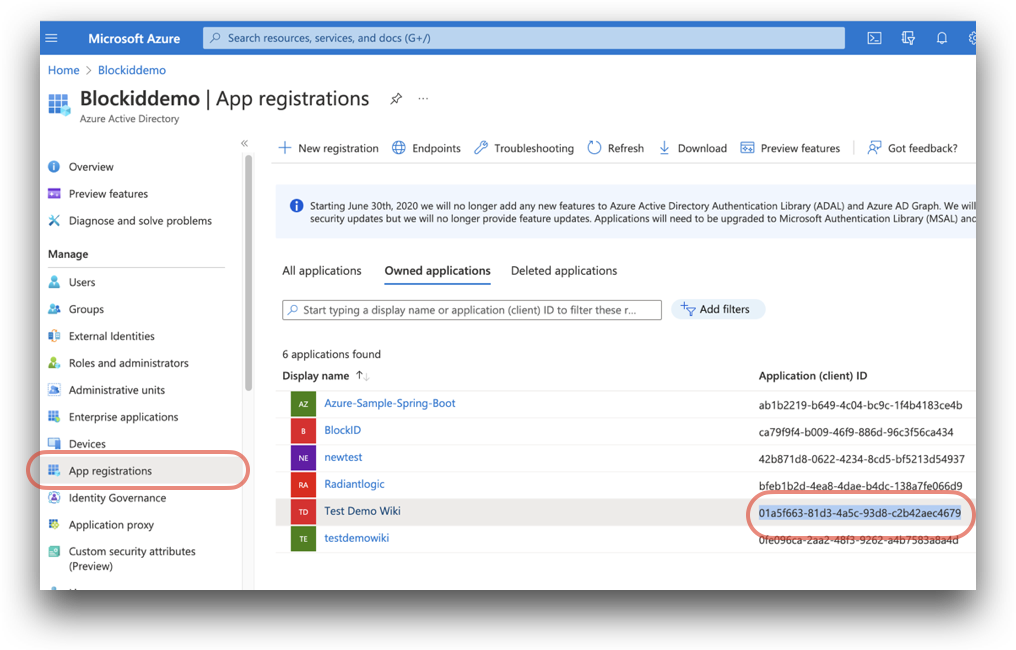
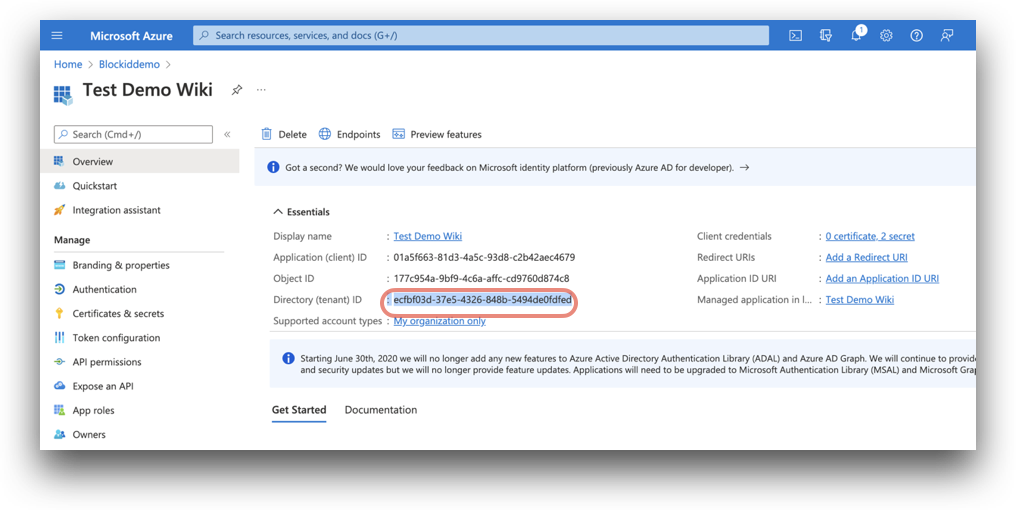
- Application (client) ID: The
application (client) IDcan be found on the App registrations page.Azure Home -> Azure Active Directory -> App registrations
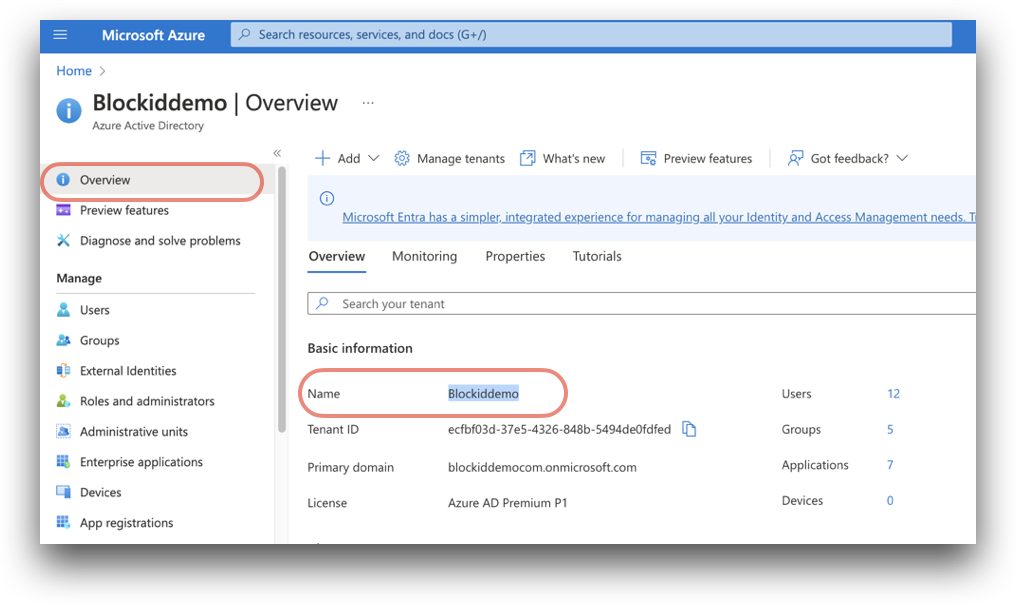
- Tenant ID: Found on the Azure Active Directory Overview page.
Azure Home -> Azure Active Directory.
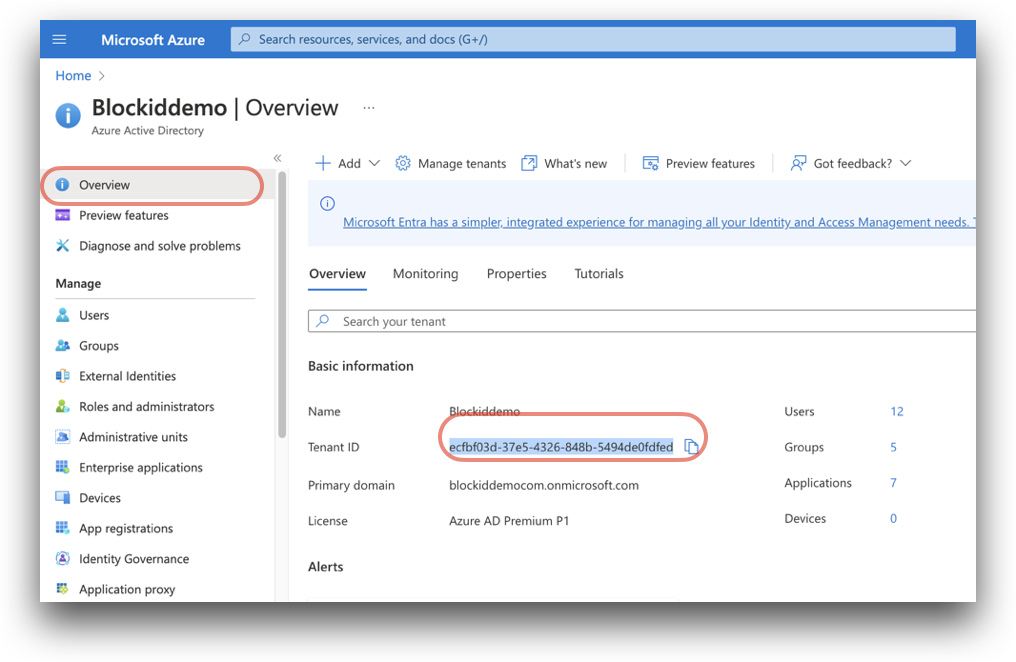
The tenant ID can also be found on [your application name] Overview, at Azure Home -> Azure Active Directory -> App registrations -> [your application name]
- (Tenant) Name: Your Azure tenant Name, Found on the Azure Active Directory Overview page.
Azure Home -> Azure Active Directory.
- Client Secret: Secret for your app registration. Located on the application Certificates and secrets page.
Azure Home -> Azure Active Directory -> App registrations -> [your application name] -> Certificates and secrets
You can only view the certificate at the time it is created. If you lost your secret, you can create a new one by clicking New client secret
Login URL: Your login URL defaults to
https://login.microsoftonline.comGraph API URL: Your Graph API URL defaults to
https://graph.microsoft.com
Setup Azure AD in AdminX
Now that all the necessary prerequisites have been completed, the final step is to connect to Azure AD using AdminX.
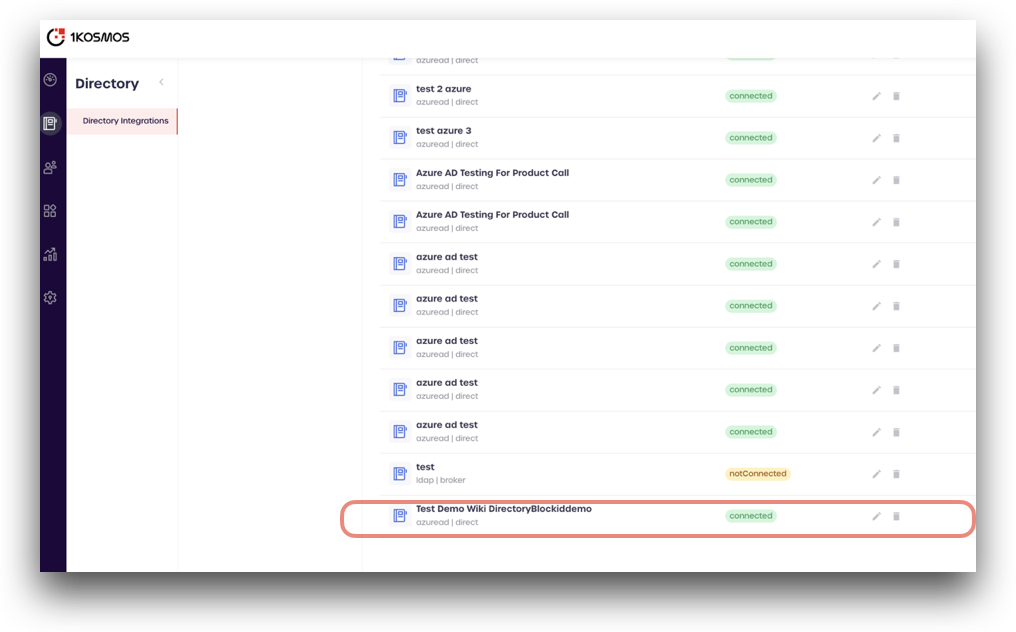
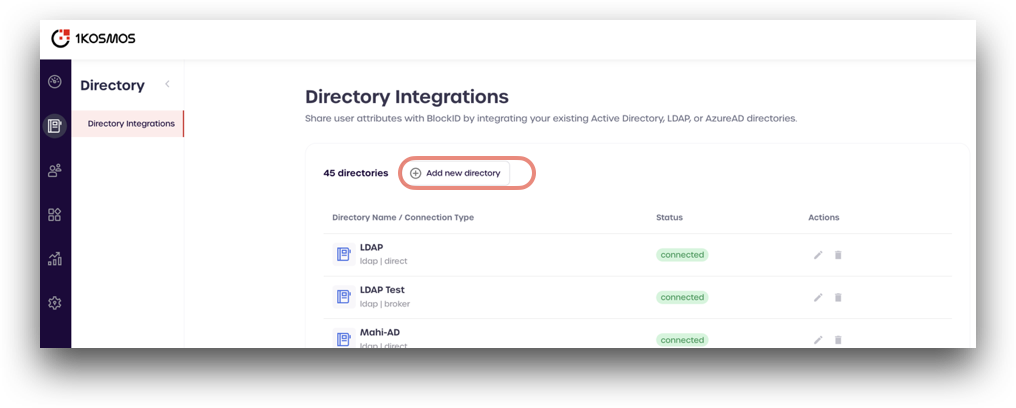
Navigate to your AdminX panel and log in as a tenant or community administrator. From the Administrator Dashboard, click on the Directory icon located on the left-hand menu.
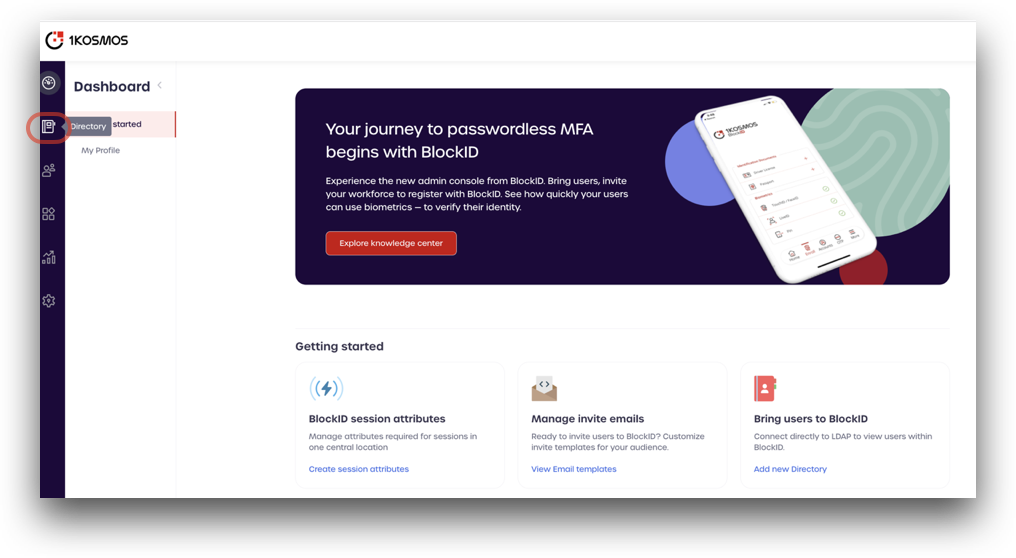
From the Directory Integrations page, click Add new directory.
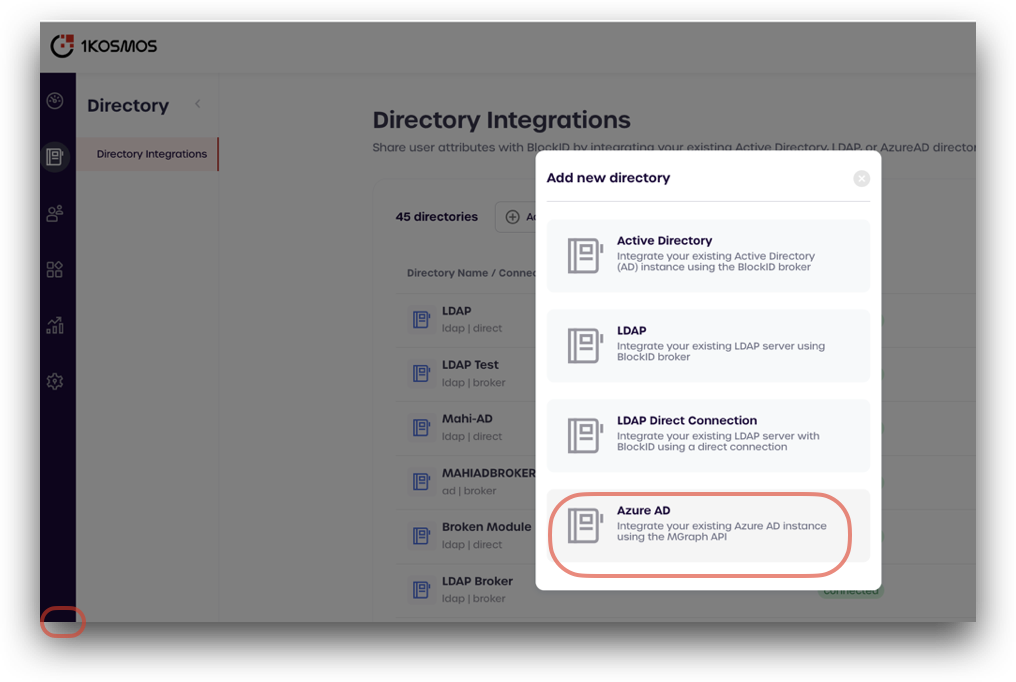
Select Azure AD
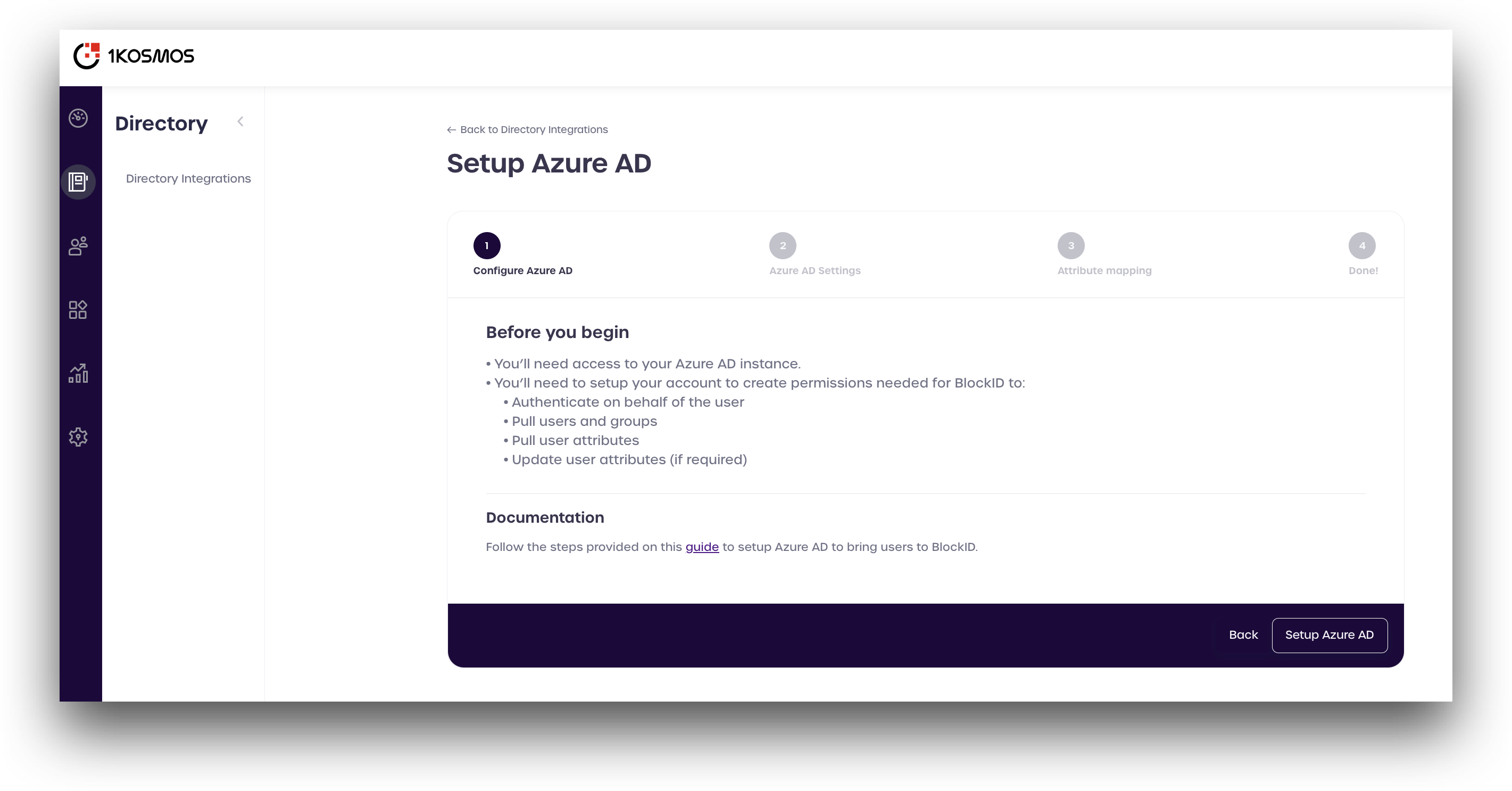
Review the information displayed, and click Setup Azure AD
Next, enter all the information you copied from Azure (please see the picture for reference).
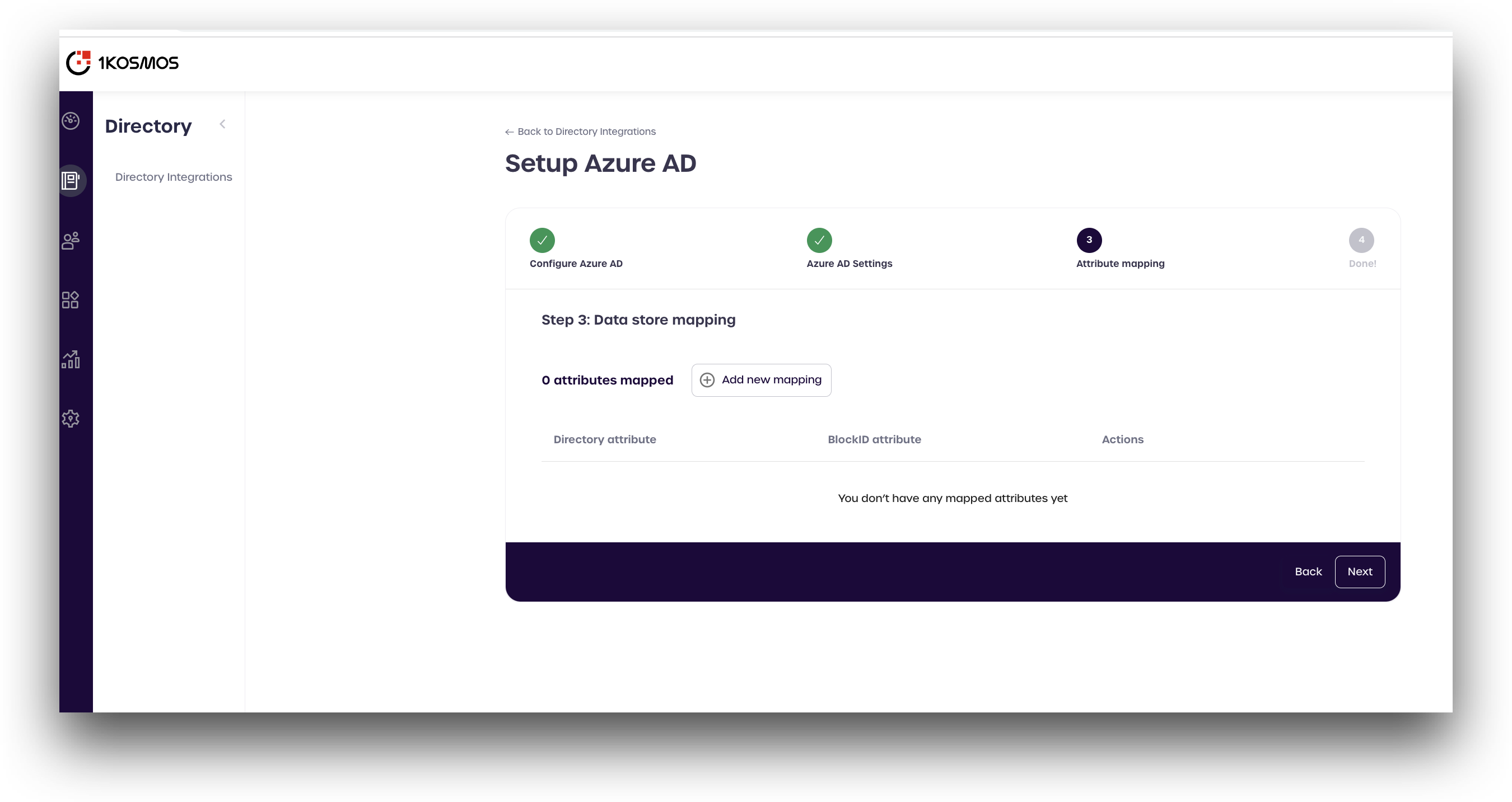
Finally, we need to configure attributes mapping for the BlockID data store used internally by AdminX. This mapping links the Azure directory attributes - such as name, number, etc. - to the attributes used by BlockID.
The following attributes need to be mapped:
| Azure Directory Attribute | BlockID Attribute Name |
|---|---|
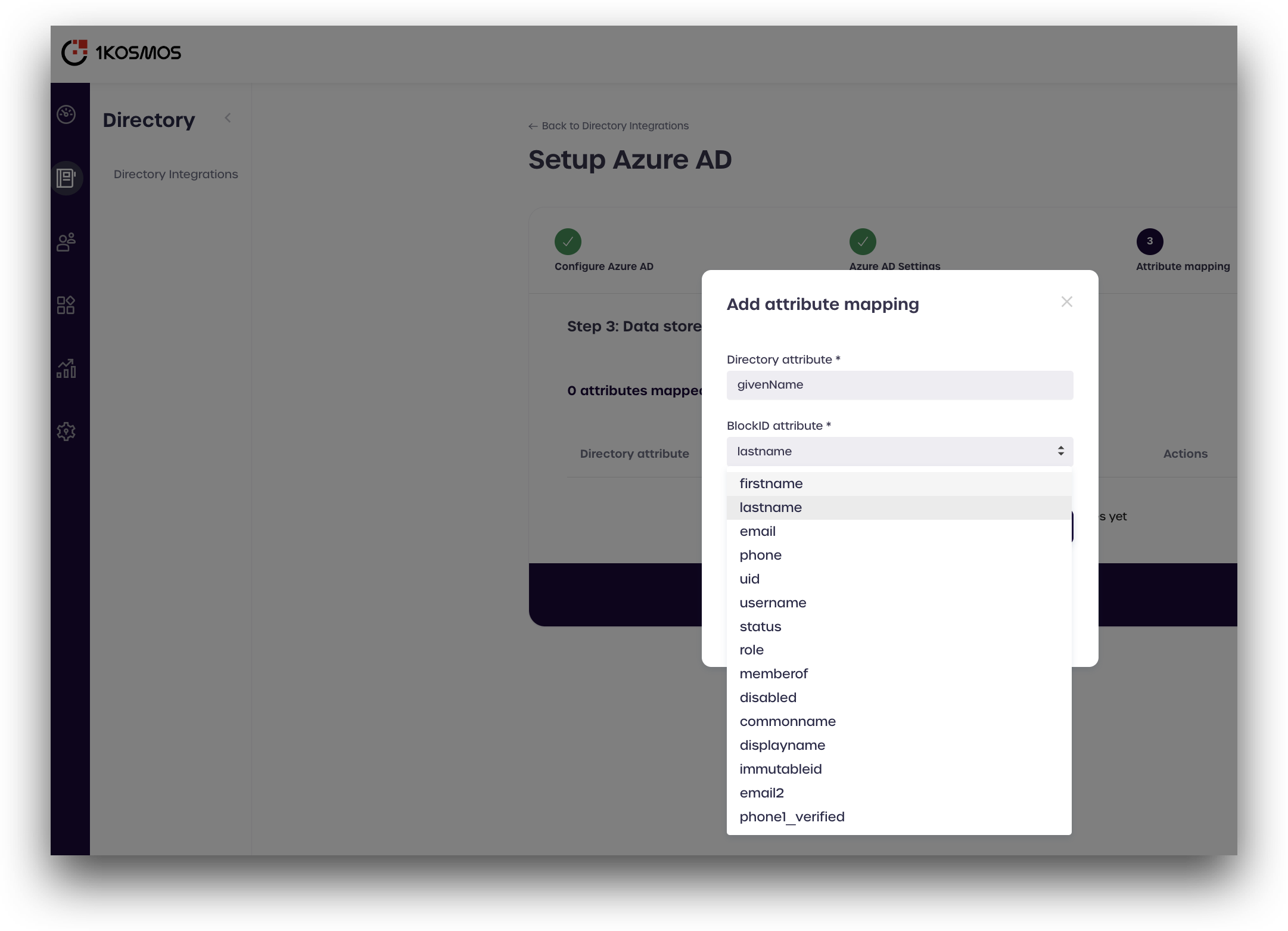
| givenName | firstname |
| surname | lastname |
| userPrincipalName | |
| mobilePhone | phone |
| userPrincipalName | username |
First, click Add new mapping
Enter the Azure attribute in the top box labeled Directory attribute. Use the drop-down menu to select the corresponding BlockID attribute from the table above, and click Create.
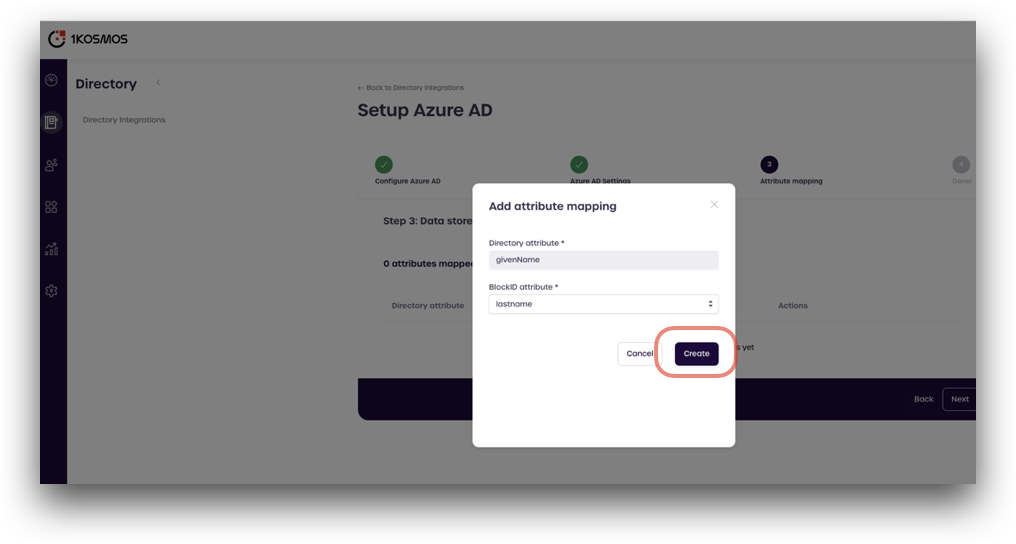
Repeat this process until all the attributes from the table above are mapped, and click Next.
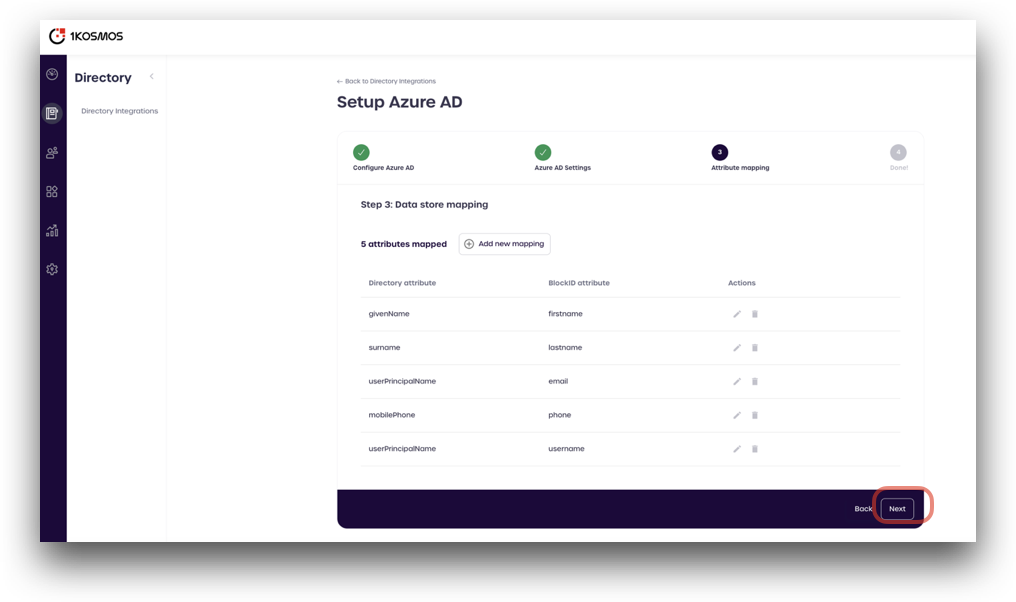
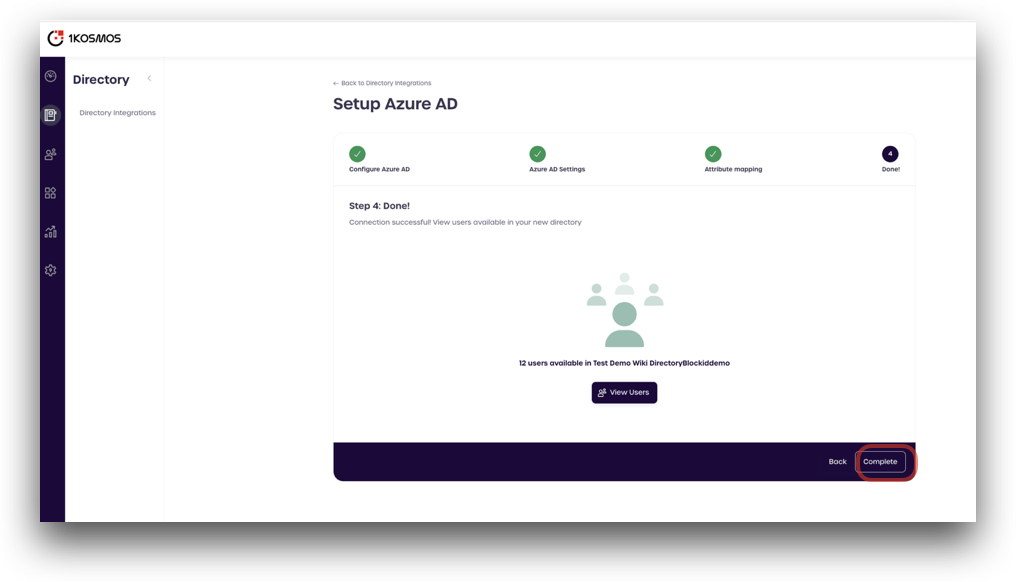
Once the attributes are mapped, you are done! You can click the View Users button to preview your Azure AD users.
Click Complete to finish adding your Azure AD directory into Adminx.
You can verify that the Azure AD directory has been added by checking the Directory Integrations page in AdminX. Your Azure directory should now be available and show as connected